Blog Posts

This solution is suited for those who host their Drupal website on a shared hosting server, whereby the primary domain on your hosting account doesn’t afford the luxury of setting up a virtualhost for your domain.

Riksbank, Sweden's central bank, is entertaining the idea of introducing its' own e-currency, as notes and coins become less relevent in favour of digital payments.
For those who have been struggling setting up a Git Server on a shared hosting environment, here is a how-to guide on setting Git Server up on Hostgator.
Older Raspberry Pi devices such as the Raspberry Pi 2, may be more vulnerable if they haven't been updated in a while.
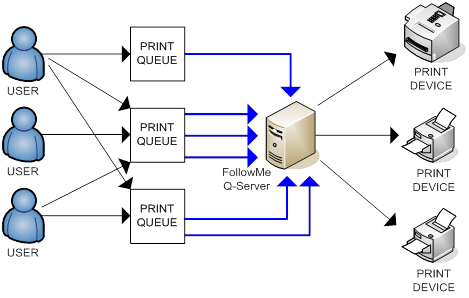
You might be aware that you can do Printer Pooling on a Windows Operating System. But did you know that you can do the same as well on Linux?
Media software from VLC, Kodi, Popcorn Time, and Stremio are vulnerable, researchers say

Say goodbye to needing an aerial - free-to-air TV streaming service Freeview is now available on Google Chromecast.

Linux containers are gaining significant ground in the enterprise, which is not surprising, since they make so much sense in today’s business environment. With that said, container technology as we know it today is relatively new, and companies are still in the process of understanding the different ways in which containers can

A coding error dubbed The Riddle has been uncovered in MySQL. This issue can be exploited by attacker powering a MITM attack to steal user accounts.
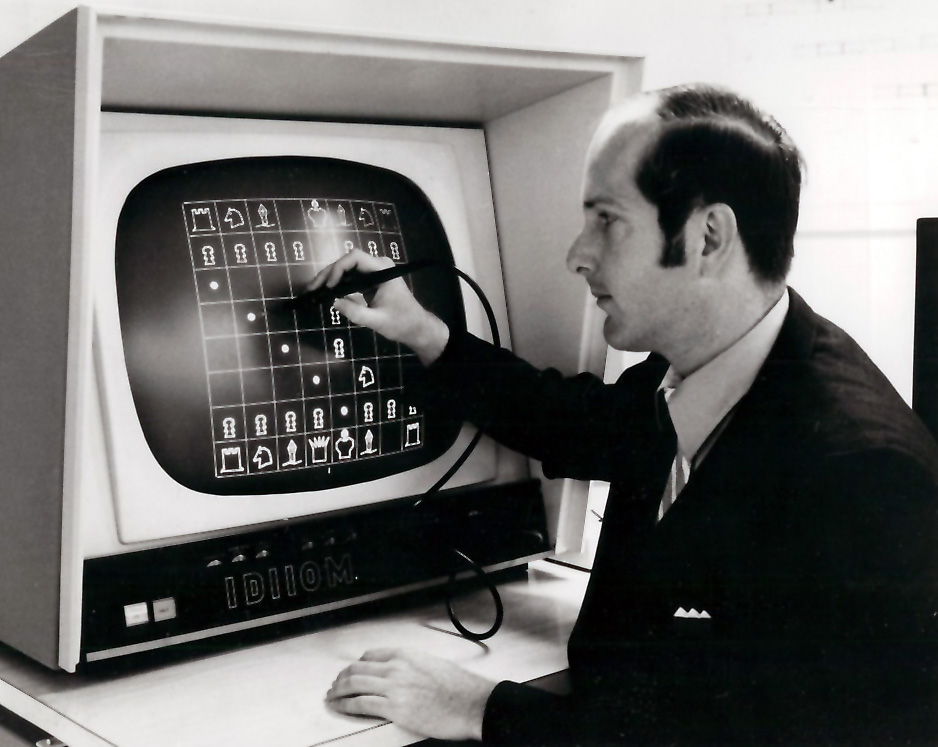
The following is a general howto to optimize your chess engine in your chess GUI,
Pagination
- Previous page
- Page 5
- Next page
Contact Info
PO Box 246
Miami QLD 4220
Australia
Email: contact@tomthorp.me
Mob: +61 (414) 298 490
Contact Card: ![]()